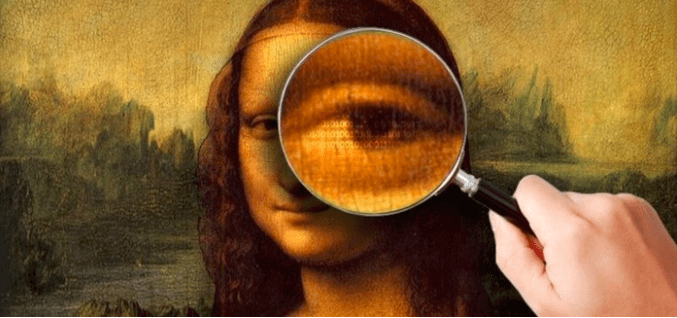
Steganography is the art of hiding messages inside an image.In a broader aspect,it is hiding messages in a file i.e. ,we are not limited to just images.It is a combination of Greek words steganos meaning “covered ,concealed, or protected” and graphien meaning “writing”.It is actually using the idea of “hiding stuff in plain sight”.it is usually used when information which if by any chance is compromised dosen’t have much consequences.Many have a misunderstanding that it is a form of encryption ,but it is in fact not.
There are countless algorithms available online which can automate the procedure.Actually it is not that hard to make an algorithm of your own as even I have made my own algorithm which I shall be sharing soon.To make a simple string hiding algorithm ,one simple principle is followed.Let us first try to implement a simple algorithm in which we try to hide the word “hi” in a small 5×2 image.

As we know each of those tuples represent a pixel and the three values contained in it are merely the frequency values of the red ,blue and green colour of the pixel.As there are ten pixels in it ,so there are total 10 tuples and 30 values with us.This entire representation is known as pixel map of an image.
Now if we want to hide “hi” inside the image then we first convert the individual letters of the string into its 8 bit binary equivalent.So h becomes 01101000 and i becomes 01101001.
Now comes the part of hiding this word inside the image.As I had said earlier ,there are several types of rules one can implement to hide the image.So for simplicity sake ,I implemented a simple rule that is :-
->First take the binary value of “h” and grab 3 pixels starting from left corner of the map.So this means now we have 9 values in our hand.
->Now map the binary equivalent value of “h” into those 9 values like this: 0 for even number and 1 for odd number.Not sure what I just said there?Here’s how we go:-
This mapping should make sense to you.To implement the rule certain changes have been made in the values. for example 48 became 47 as 1 was encountered .Similarly 128 became even to accommodate the fact that 0 was mapped into it.

If you remember correctly we had grabbed 9 values and we have mapped 8 of them with the character “h”.Then what does the 9th value do?The 9th value is the deciding value which decides whether the revealing of secret message should go on or stop.It is mapped even if it should go on and odd if it should stop.In our case the revealing still hasn’t stopped as we still have the letter “i” i.e. the revealing shouldn’t stop so the 9th value should be even.Since 68 is already even ,so no change is implemented.
->In a similar fashion the next three pixels are taken and the same thing is done for the next character in the string till the end of the string is reached.
It might be a little hard to understand in the beginning but if you read it a couple of times more,probably you would get it when I said countless algorithms can be implemented.
If you implemented “i” as well then just compare the obtained pixel map with the original pixel map.You wont find much difference in values of the r,g,b values. Further more ,if this was implemented in a real image no visible difference would be observed as most images are made up of thousands of pixels.
So this should give you a basic idea of how you can hide a message in an image.Obviously one last thing which should be kept in mind is that your receiver should know your method of hiding so that he can extract the message.Another interesting concept is hiding an image in another image which I shall be posting anytime soon.So stay tuned!
All Rights Reserved for Arnav Tripathy
