A new attack called Plundervolt gives attackers access to the sensitive data stored in a processor’s secure enclave.
When thieves want to steal treasures surrounded by sensors and alarms, they sometimes resort to cutting the power, disrupting the flow of electricity to those expensive security systems. It turns out that hackers can pull off a similar trick: breaking the security mechanisms of Intel chips by messing with their power supply, and exposing their most sensitive secrets.
Two teams of researchers—one at the University of Birmingham in the UK, TU Graz in Vienna, KU Leuven in Belgium and another at the Technische Universität Darmstadt in Germany and the University of California—have found a new technique that can allow hackers to fiddle with the voltage of Intel chips to cause them to leak information stored using Intel’s Secure Guard Extensions feature. Those “secure enclaves” in a device’s memory are designed to be impregnable. Intel, which asked the teams to keep their findings under wraps for the last six months, confirmed the findings and pushed out an update to its chip firmware to prevent the attack today.
The technique, which one of the two teams calls Plundervolt, involves planting malicious software on a target computer that temporarily reduces the voltage of the electricity flowing to an Intel chip. That drop in voltage, known as “undervolting,” typically allows legitimate users to save power when they don’t need maximum performance. (By that same token, you can use the voltage-variance feature to “overclock” a processor for more intensive tasks.) But by momentarily undervolting a processor by 25 or 30 percent, and precisely timing that voltage change, an attacker can cause the chip to make errors in the midst of computations that use secret data. And those errors can reveal information as sensitive as a cryptographic key or biometric data stored in the SGX enclave.
“Writing to memory takes power,” says Flavio Garcia, a computer scientist at the University of Birmingham who, along with his colleagues, will present the Plundervolt research at IEEE Security and Privacy next year. “So for an instant, you reduce the CPU voltage to induce a computation fault.”
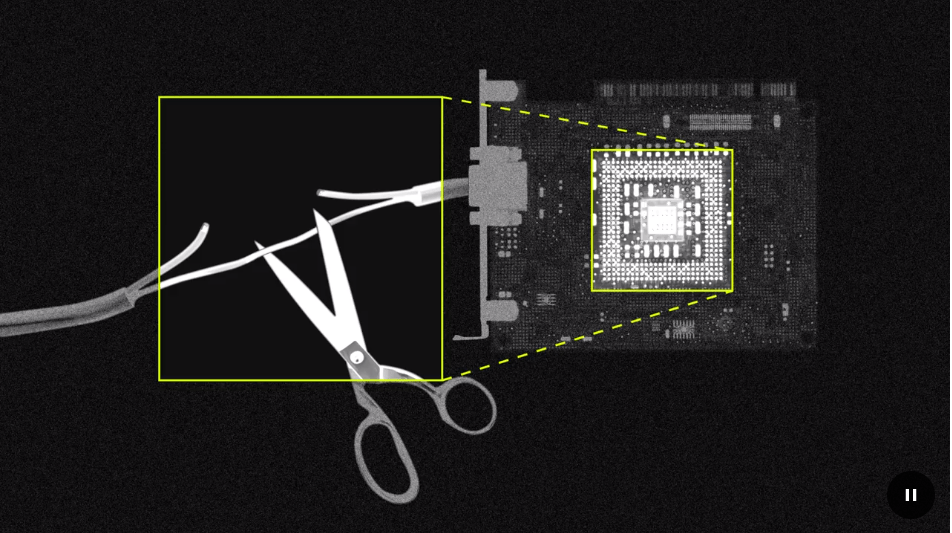
Once the researchers found that they could use voltage changes to induce those faults—a so-called fault injection or “bit flip” that turns a one to a zero in the SGX enclave or vice versa—they showed that they could also exploit them. “If you can flip bits when, for instance, you’re doing cryptographic computations—and that’s where this gets interesting—you can recover the secret key,” Garcia says. In many cases, the researchers explain, changing a single bit of a cryptographic key can make it vastly weaker, so that an attacker can both decipher the data it encrypts and derive the key itself. You can see the impact on an AES encryption key here:
The researchers also showed that they could use those bit flips to make the processor write to an unprotected portion of memory rather than to the secure SGX enclave:
The researchers acknowledge that their attack isn’t exactly easy to pull off. For it to work, the attacker has to have already somehow installed their malware with high-level, or “root,” privileges on the target computer. But Intel has advertised its SGX feature as preventing corruption or theft of sensitive data even in the face of this sort of highly privileged malware. The researchers say they have demonstrated a serious exception to that guarantee.
“Intel says this enclave will protect calculations even from someone on the same system who has root,” says Kit Murdock, one of the Birmingham researchers. “But we can still flip bits even inside what should be a safe enclave.”
The Birmingham, TU Graz, and KU Leuven researchers’ work follows findings from a group of researchers at the University of Tsinghua in Beijing and the University of Maryland, who presented a similar technique at the Association for Computing Machinery conference earlier this month. That technique, which the Tsinghua and Maryland researchers called VoltJockey, used voltage changes to undermine the security of processors in much the same way as Plundervolt, but focuses on chips from ARM chips rather than Intel.
Plundervolt is hardly the first time Intel’s SGX feature has been broken. Other earlier attacks like Spectre and Foreshadow, which both exploited the speculative execution feature of Intel’s chips, could also in some cases break the confidentiality of the Intel’s SGX enclaves before the chipmaker released firmware patches to prevent them. Earlier this year, researchers at TU Graz even showed that they could plant their own malware inside of the SGX enclave using a technique known as return-oriented programming, making it invisible to antivirus software.
The Plundervolt researchers reached out to Intel last June about their findings, and Intel wrote in a security advisory today that a third team of researchers from the Technische Universität Darmstadt and the University of California also reported the undervolting technique to the company around the same time. Intel says the VoltJockey team—despite their conference talk’s focus on ARM chips—also warned Intel about the issue two months later.
In response, Intel today pushed out an update to its chips’ firmware that by default locks the voltage settings of its processors, blocking the undervolting attack. “Intel has worked with system vendors to develop a microcode update that mitigates the issue by locking voltage to the default settings,” a blog post from Intel published today reads. “We are not aware of any of these issues being used in the wild, but as always, we recommend installing security updates as soon as possible.”
Intel declined to detail how the patch will affect overclockers. But locking those power settings may be a healthy tradeoff to prevent an insidious attack that uses those same voltage switches to seduce your processor into spilling its secrets.
All Rights Reserved for Andy Greenberg
